5 of 5 free uses remaining today
Phishing Investigation Toolkit
The complete SOC analyst playbook for investigating phishing emails. 52-page guide, Excel investigation log, and quick reference card — built by practitioners, verified against industry standards.
Referenced against NIST SP 800-61, MITRE ATT&CK, and 25+ free tools.
Phishing is the #1 attack vector. Are you investigating it properly?
91% of cyberattacks start with a phishing email. Yet most security teams rely on ad-hoc investigation methods — no structured process, no documentation trail, no consistent risk scoring. When an incident escalates, there's no evidence package ready for management or legal.
No Structured Process
Ad-hoc investigation leads to missed indicators and inconsistent outcomes.
Slow Response Times
Without a workflow, analysts waste time deciding what to check next.
No Documentation Trail
When incidents escalate, there's no evidence package for management.
What You Get
Three professional-grade deliverables that work together as a complete investigation system.
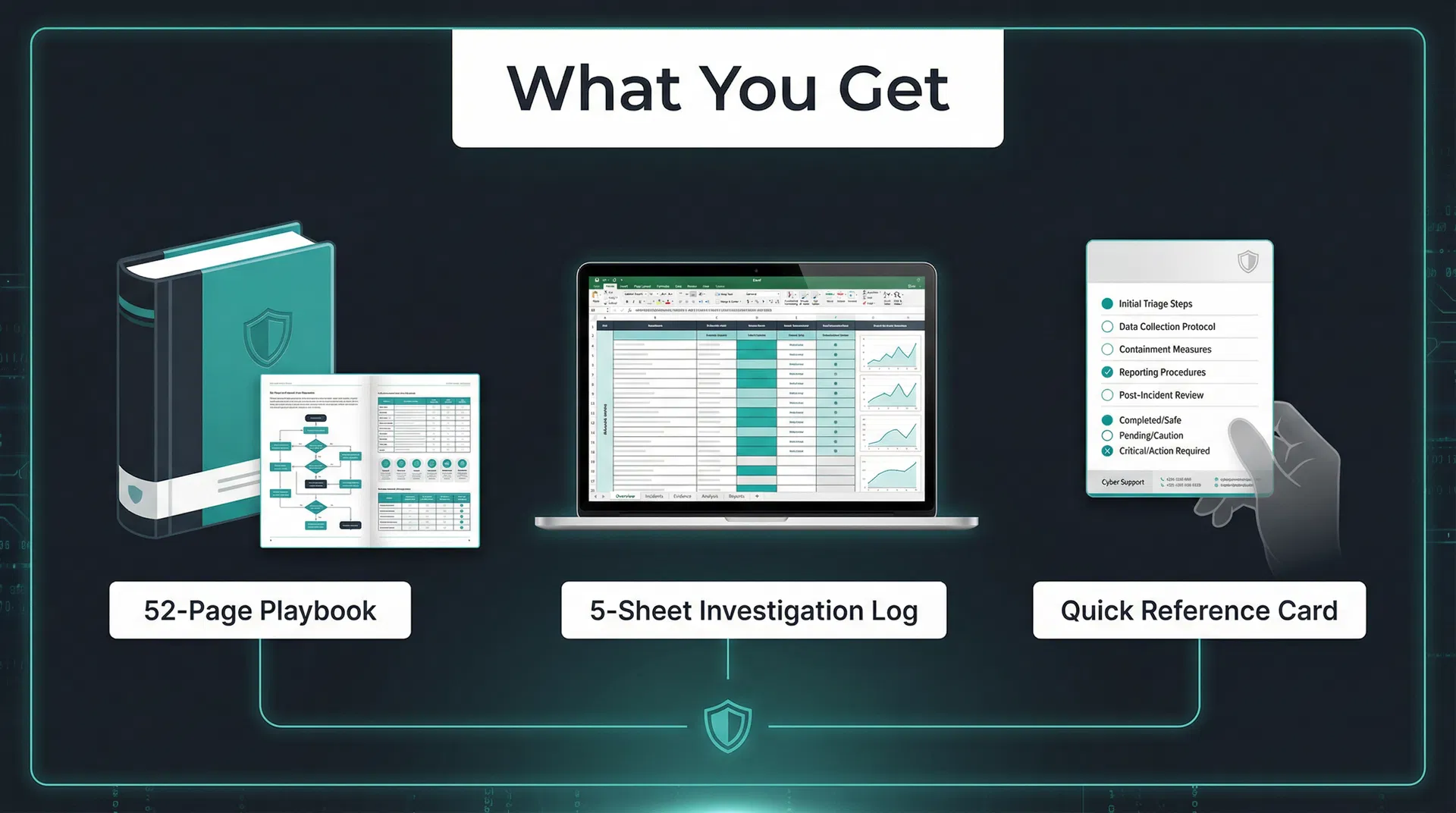
52-Page Playbook
PDF with 11 embedded diagrams
- 10-phase investigation workflow
- Email header analysis guide
- SPF/DKIM/DMARC verification
- URL deobfuscation techniques
- Attachment risk assessment
- MITRE ATT&CK mapping
- Escalation decision trees
- 25+ free tool references
5-Sheet Investigation Log
Excel with auto-calculations
- Investigation Log with dropdowns
- IOC Tracker (domains, IPs, URLs, hashes)
- Risk Score Calculator (13 factors, max 131)
- MITRE ATT&CK Mapping sheet
- Investigation Timeline
- Conditional formatting
- Auto-calculated risk levels
- Print-ready layout
Quick Reference Card
Printable desk reference
- 10 phishing indicators
- Rapid triage checklist
- Key tools with direct links
- Authentication quick check
- File risk levels by extension
- Containment actions
- MITRE ATT&CK quick reference
- Fits on one printed page
Inside the Playbook: 10-Phase Investigation Workflow
Every phase is a structured step with decision points, tool recommendations, and documentation requirements.
Initial Triage & Classification
Rapid assessment of the reported email to determine priority and investigation scope.
Email Header Analysis
Parse Received chains, verify From/Return-Path/Reply-To consistency, identify originating IP.
Authentication Verification
Check SPF, DKIM, and DMARC results to determine if the sender is authorised.
URL & Link Analysis
Extract, deobfuscate, and safely analyse all URLs using sandboxed tools.
Attachment Analysis
Assess file risk levels, check hashes against threat intelligence, sandbox suspicious files.
Sender Reputation Assessment
Domain age, WHOIS data, blacklist checks, and historical sending patterns.
Content & Social Engineering Analysis
Identify manipulation techniques, urgency triggers, and impersonation patterns.
IOC Extraction & Documentation
Extract all Indicators of Compromise and map to MITRE ATT&CK techniques.
Verdict & Escalation
Risk score calculation, escalation decision tree, and containment actions.
Post-Investigation Actions
Lessons learned, detection rule creation, and process improvement.
What's Inside
Professional-quality content you can use on day one.
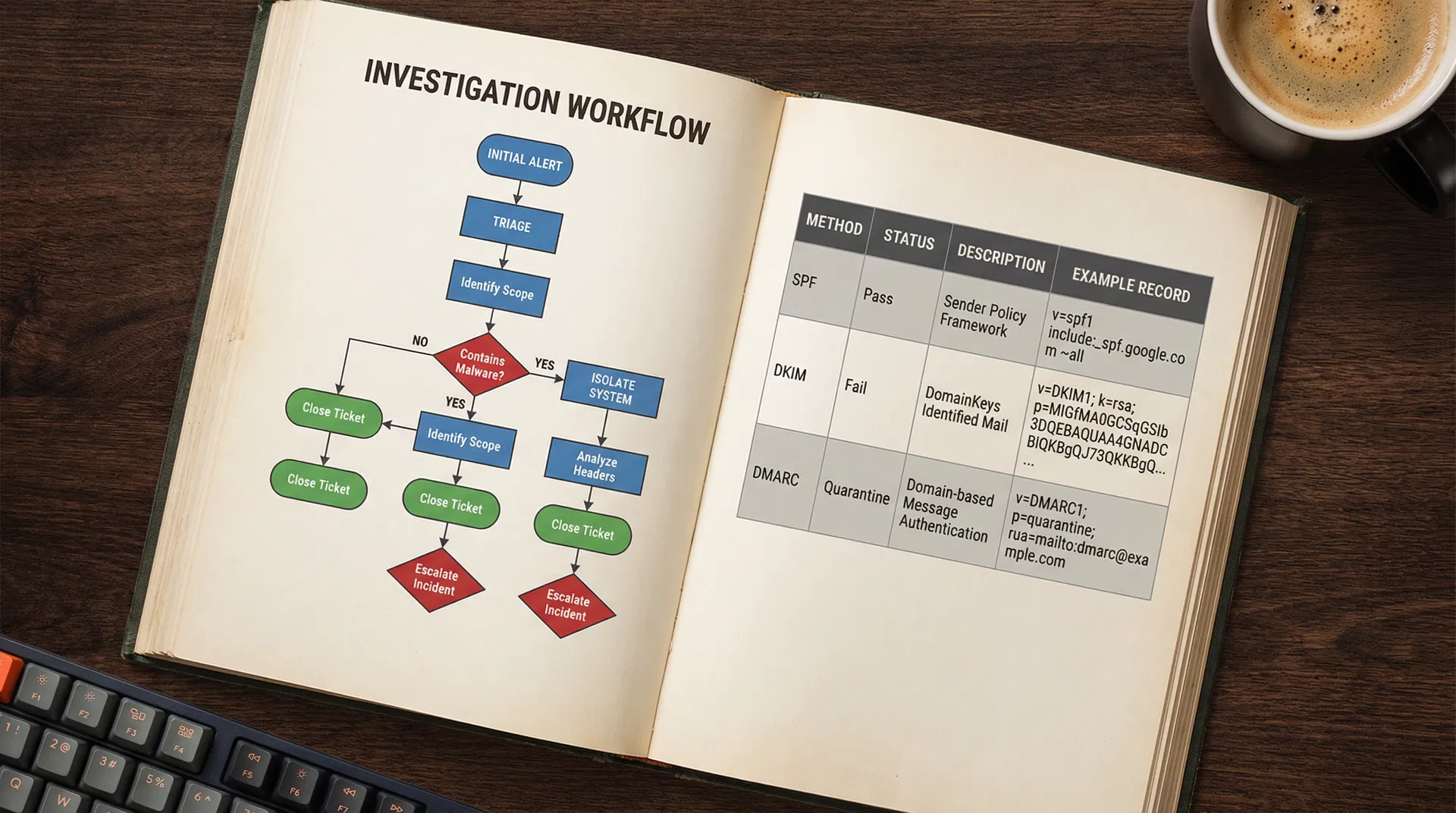
Sample pages showing investigation workflow and SPF/DKIM/DMARC reference table
11 professional diagrams embedded throughout the playbook
25+ Free Tools Referenced
Every tool in the playbook is free and publicly accessible. No paid subscriptions required.
Built For Security Professionals
SOC Analysts
L1–L3 analysts investigating phishing alerts daily
IT Managers
SME security leads who are the de facto security team
Consultants
Need professional-grade deliverables for client work
Help Desk Leads
Training staff on structured email triage
Verified Against Industry Standards
NIST SP 800-61 Rev. 2
Computer Security Incident Handling Guide
MITRE ATT&CK
Phishing techniques T1566.001–T1566.003
RFC 5322 / 7208 / 6376 / 7489
Email authentication protocol standards
Microsoft IR Playbook
Official phishing investigation procedures
What Professionals Say
Early access feedback from security professionals.
"Finally, a structured process I can follow for every phishing alert. The investigation log alone saves me 20 minutes per case."
SOC Analyst, L2
Financial Services
"We used the playbook to train our help desk team. The quick reference card sits on every desk now."
IT Security Manager
Healthcare SME
"I use the investigation log as a deliverable for my clients. Professional quality, saves me building my own templates."
Cybersecurity Consultant
Independent
Choose Your Licence
Both licences include all three components with free lifetime updates.
Individual
- 52-page Playbook PDF
- 5-sheet Investigation Log
- Quick Reference Card
- Free lifetime updates
- Single user licence
Team
- Everything in Individual
- Up to 10 team members
- Organisation-wide distribution
- Free lifetime updates
- A$14.90 per user
Use code LAUNCH20 at checkout for 20% off.
Frequently Asked Questions
30-Day Money-Back Guarantee
If the toolkit does not meet your expectations, contact us within 30 days for a full refund. No questions asked. We are confident you will find it valuable.